Earlier in November I was speaking as part of a track on cybersecurity at (Virtual) Electronica, a tradeshow held every two years in Munich. One of the questions related to when open source hypervisors will appear at the heart of mission critical systems. Mission critical systems are those that simply have to work all the time in a predictable way. Relevant applications include avionics, rail infrastructure, self- driving vehicles.
Almost every popular open source hypervisor (E.g. Xen, KVM, seL4) has been used to demonstrate the ability to host virtual security appliances, facilitate secure software updates, and partition system designs to reduce attack vectors compared to operating system (OS)-based designs.
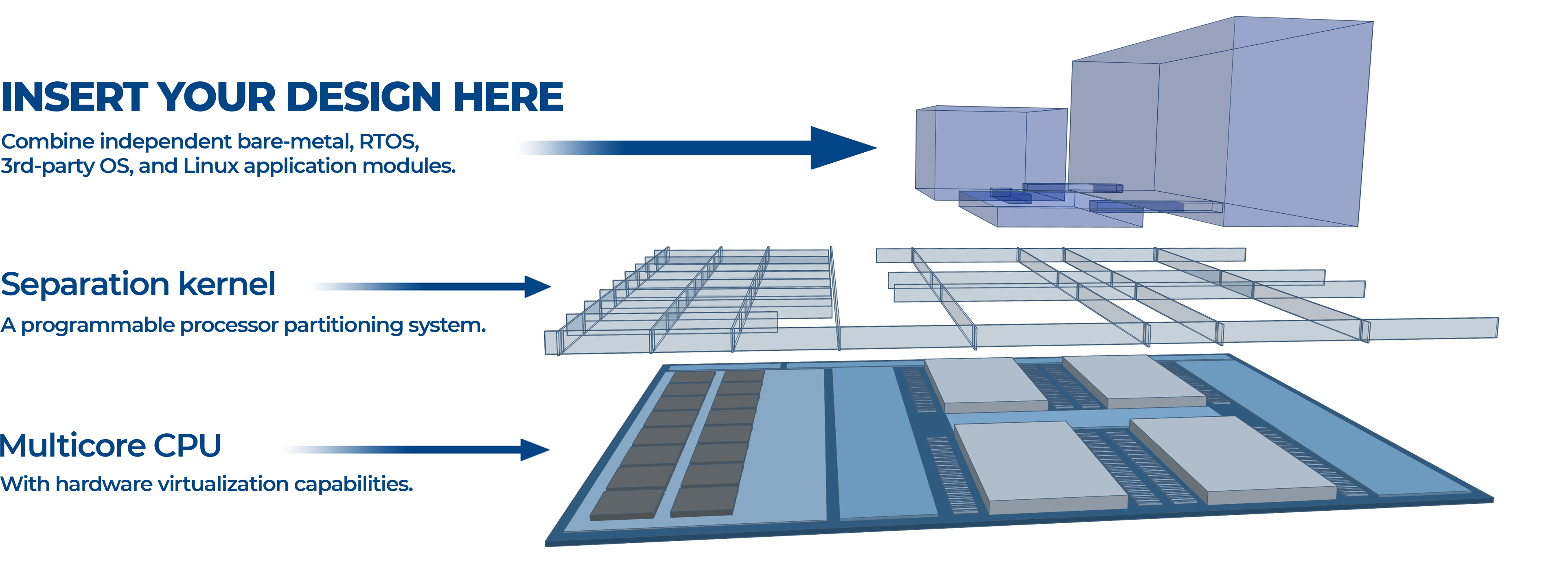
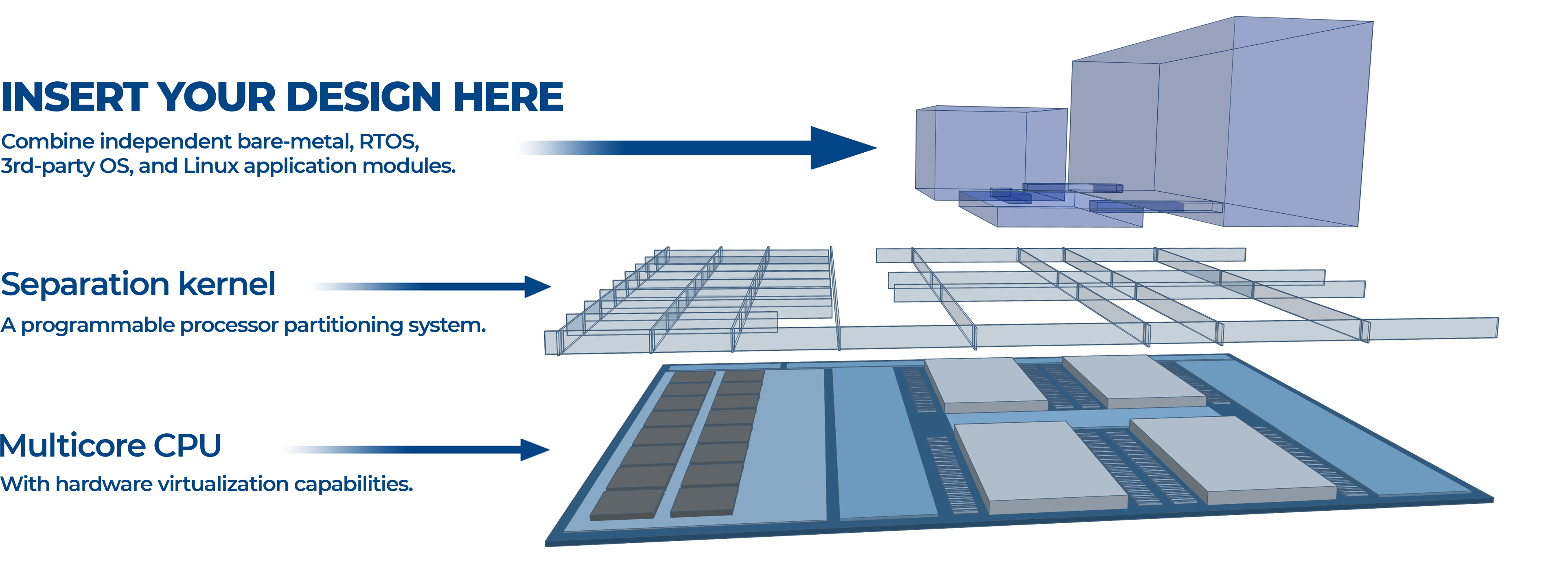
At a high-level, the ability to partition hardware and software, and provide virtual networking, has become a commoditized property afforded by hypervisors. From our discussions with customers and, indeed, institutions like the US Army, fundamental gaps are revealed which must be addressed in order to realize the vision of autonomous mission systems. Primarily they fit into three main themes;
- Real-time Suitability; As companies consolidate system functionality on single multicore processors to reduce cost, power and footprint, legacy software will need to be ported while maintaining underlying platform assumptions when transitioning from real to virtual/emulated hardware. Time-sensitive interfaces must be carefully managed to preserve timing characteristics. Placing operating systems on hypervisors introduces layers of abstraction
- Validation of System Properties; Gaining confidence in the assurance of safety and security properties of software systems has become incredibly difficult as designs have reached overwhelming levels of complexity. Technologies such as the seL4 microkernel have successfully provided proof of correctness and resiliency of hypervisor functionality (E.g. adding/removing VMs). But system integrators are still left with a tremendous burden of developing/integrating the complex software stacks needed to implement the application platform dependencies (E.g. filesystems, IP networking). Many industry solutions fail to help the verification of system integration correctness and overarching validation of acceptable system behavior
- Safety & Security Certification; Almost every large-scale mission critical system is subject to safety regulations to ensure passengers and bystanders are reasonably protected from catastrophic failures due to integrity or security vulnerabilities. Manufacturers adhere to stringent software development standards prescribed in standards such as avionic DO-178C DAL A and automotive ISO26262 ASIL-D
These are the areas where we focus the LYNX MOSA.ic framework, on which we construct a number of specific-to-application products for Avionics, UAVs/Satellites and Industrial markets.
Open source has clearly made great inroads into a diverse range of applications. We see open source used in avionics platforms, but sand boxed to implement specific system features that are unrelated to the must work all of the time in a predictable way functionality. I think we will see increasing adoption of open source in the long term and will need a software company to implement a business model analogous to what RedHat has done to drive Linux adoption across Enterprises.
If you want to know more about what Lynx discussed at Virtual Electronica, read this piece here.


 Ian Ferguson | VP Marketing
Ian Ferguson | VP Marketing