- Home
- Solutions
- Lynxelement
LynxElement: Design for Minimalism and Determinism
Transition from heavyweight operating systems to purpose-built runtimes. With LYNX MOSA.ic™ deploy applications as LynxElement unikernels, reducing your system's code base and simplifying your path to safety assurance.



What is a Unikernel?
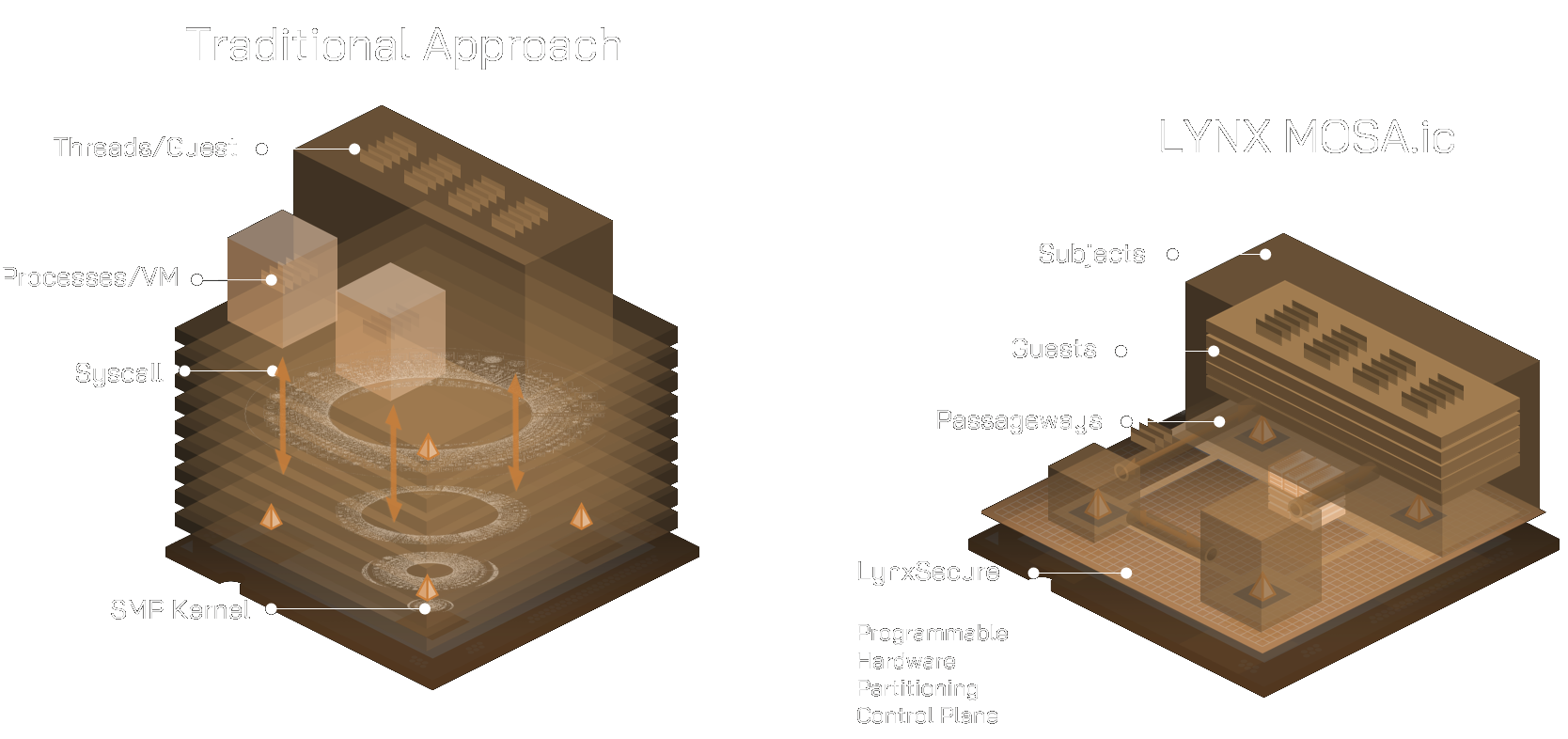
In conventional computing architectures, applications operate atop large, general-purpose operating systems containing extensive drivers and services that are not required for the application’s intended function. This unnecessary functionality increases system complexity, expands the attack surface, and complicates safety certification efforts.
A unikernel architecture fundamentally changes this model. It compiles the application together with only the operating system components strictly required for execution. The result is a single-purpose, lightweight, bootable image that offers improved performance, reduced attack surface, and significantly simplified verification for safety-critical deployments.
What is a Unikernel?
In conventional computing architectures, applications operate atop large, general-purpose operating systems containing extensive drivers and services that are not required for the application’s intended function. This unnecessary functionality increases system complexity, expands the attack surface, and complicates safety certification efforts.
A unikernel architecture fundamentally changes this model. It compiles the application together with only the operating system components strictly required for execution. The result is a single-purpose, lightweight, bootable image that offers improved performance, reduced attack surface, and significantly simplified verification for safety-critical deployments.
Why LynxElement and Why Now
Mission- and safety-critical markets are undergoing structural change. Platforms in space systems, unmanned systems, and autonomous mobility are transitioning from monolithic architectures to modular, purpose-built software components.
At the same time, cybersecurity threats continue to escalate, and multicore interference presents growing certification challenges. These conditions demand a pragmatic, minimal, and well-bounded runtime environment that supports credible safety cases while enabling accelerated deployment cycles.
Why LynxElement and Why Now
Mission- and safety-critical markets are undergoing structural change. Platforms in space systems, unmanned systems, and autonomous mobility are transitioning from monolithic architectures to modular, purpose-built software components.
At the same time, cybersecurity threats continue to escalate, and multicore interference presents growing certification challenges. These conditions demand a pragmatic, minimal, and well-bounded runtime environment that supports credible safety cases while enabling accelerated deployment cycles.
Enabling IMA Beyond Traditional Avionics
Integrated Modular Avionics (IMA) principles are no longer confined to commercial cockpit systems. Strong isolation, modular deployment, and bounded execution models are increasingly required across defense, space, and autonomous platforms.
LynxElement extends these principles beyond traditional avionics domains. By reducing cross-domain interference and simplifying resource analysis, it enables scalable and economically viable certification strategies for emerging markets where cost, speed, and safety must coexist.
Because each image is small and purpose-built, changes can be implemented, rebuilt, and redeployed quickly without impacting unrelated system components. This enables rapid iteration, streamlined updates, and more efficient re-certification when modifications are required.
The Core Differentiator
Where traditional RTOS platforms emphasize feature breadth, LynxElement prioritizes disciplined minimalism. This strategic focus reduces complexity and strengthens both security and certification outcomes.
| Feature | The Traditional RTOS Approach | The LynxElement Approach |
|
Footprint |
Feature-rich, but often bloated with unused services. | Minimalist. Purpose-built for the specific task. |
| Complexity |
High complexity increases certification risk. | Low complexity increases system predictability. |
| Security | Security layers added on top of the OS. | Security-first design via attack surface reduction. |
| Analysis | Difficult multicore and timing analysis. | Simplified traceability and resource analysis. |
The Core Differentiator
Where traditional RTOS platforms emphasize feature breadth, LynxElement prioritizes disciplined minimalism. This strategic focus reduces complexity and strengthens both security and certification outcomes.
Footprint:
- Traditional RTOS Approach: Feature-rich, but often bloated with unused services.
- LynxElement Approach: Minimalistic and purpose-built for the specific task.
Complexity:
- Traditional RTOS Approach: High complexity increases certification risk.
- LynxElement Approach: Low complexity increases system predictability.
Security:
- Traditional RTOS Approach: Security layers added on top of the OS.
- LynxElement Approach: Security-first design via attack surface reduction.
Analysis:
- Traditional RTOS Approach: Difficult multicore and timing analysis.
- LynxElement Approach: Simplified traceability and resource analysis.

Built for Purpose Build Applications
Modern architectures rely on modular systems composed of small, focused applications. LynxElement provides an optimized execution environment for these isolated functions.
-
Deterministic Isolation: Ensures your most critical functions do one job reliably without interference.
-
Modular Evolution: Update or replace individual software units without the need to recertify the entire system stack.
-
Fast Integration: Drastically reduces the time from development to deployment.
Built for Purpose Build Applications
Modern architectures rely on modular systems composed of small, focused applications. LynxElement provides an optimized execution environment for these isolated functions.
-
Deterministic Isolation: Ensures your most critical functions do one job reliably without interference.
-
Modular Evolution: Update or replace individual software units without the need to recertify the entire system stack.
-
Fast Integration: Drastically reduces the time from development to deployment.

Minimalism Over Excess
In a market saturated with feature-dense RTOS platforms, LynxElement offers a fundamentally different proposition: precision over excess.
It is designed for organizations that prioritize:
- Security-First Design (Not an add-on)
- Certification Efficiency (Reduced codebase)
- Minimalist Footprint (Lower complexity)
- Pragmatic Safety Assurance (Flexible and fast)
Minimalism Over Excess
In a market saturated with feature-dense RTOS platforms, LynxElement offers a fundamentally different proposition: precision over excess.
It is designed for organizations that prioritize:
- Security-First Design (Not an add-on)
- Certification Efficiency (Reduced codebase)
- Minimalist Footprint (Lower complexity)
- Pragmatic Safety Assurance (Flexible and fast)
Design for Minimalism and Determinism
Transition from heavyweight operating systems to a purpose-built runtime. Learn how to leverage LynxElement within the LYNX MOSA.ic framework to reduce your system’s code base and simplify certification.