Global armed services are looking at strategies and techniques to open up systems and reduce vendor lock. These programs are often deployed for decades, so these architectures need to be resistant to changes in the supply chain, capable of advancing functionality to keep systems globally competitive against all adversaries, and functionally safe and secure. Virtually every presentation from the US Armed Services is driving a Modular Open Systems Approach (MOSA), and includes acronyms like FACE (Future Airborne Capability Environment), SOSA (Sensor Open System Architecture), and other open capability standards.
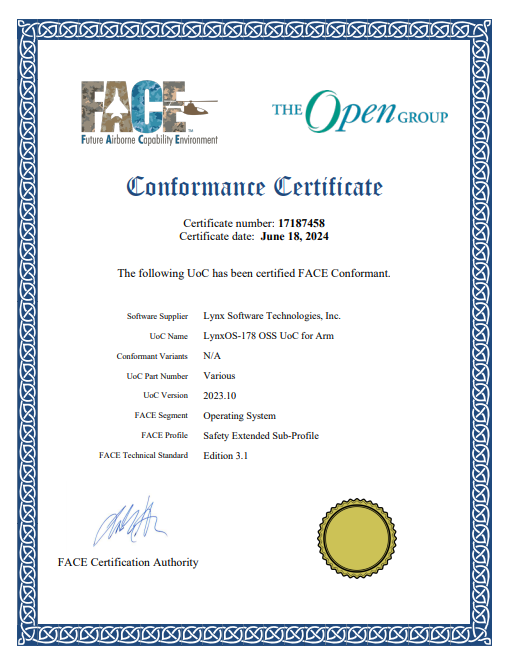
Earlier this week, we received confirmation from the Future Airborne Capability Environment (FACE) Consortium that LynxOS-178, our DAL A certified real-time operating system, had passed the conformance testing for version 3.1 of the FACE specification for two processor architectures: Arm and Intel.
If you are new to FACE, this article by our VP of Engineering provides a great background and is a quick read.
This white paper discusses that a supplier cannot simply claim FACE conformance. Instead, the process mandates a 3rd party verification authority (VA) to perform the testing. The FACE Conformance Program provides the conformance criteria and processes necessary to ensure that UoCs (Unit of Conformance – In our case, this is a software component) are developed according to the FACE Technical Standard. These criteria and processes require the verification, certification, and registration of the UoC. In our case, we chose LDRA as our VA.
|
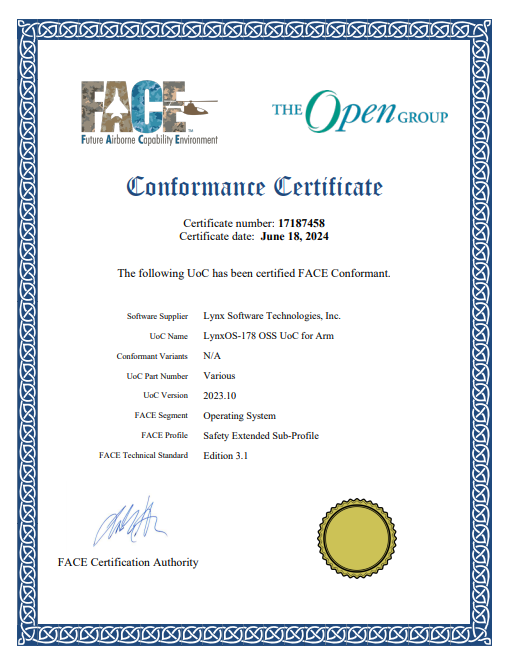
Click each image to download the PDF
|

|
We have to be careful, though, not to think that our work is done by simply aligning to standards. While they describe interfaces of libraries that applications can link into to use operating system services, these interfaces only include descriptions for software that can run in the user application space. The standards lack descriptions of expected behavior and side effects that can inform real-time and hazard analysis. They do not account for the system information needed to build, integrate, and configure a comprehensive system to behave correctly. They also do not cover software components that reside in the operating system itself, such as drivers and health monitors.
Those are the areas where Lynx focuses on delivering differentiated standards-based platforms through:
- LynxSecure which enables architects to partition resources and allocate components as individual virtual machines, and
- LynxElement (Unikernel) which can be used as the runtime environment for each individual component instead of traditional guest OSs to improve resource utilization and timing properties
Some great reading on how these can assist system architects can be found in this article written by Will Keegan (page 26 of this edition of Military Embedded).


 Lynx Software Technologies
Lynx Software Technologies